- I used NOOBS to initially install Raspbian linux (jessie)
- I wanted to set up 2 of them, one on my internal network and one on my DMZ, so I bought/configured two of everything.
- It’s then an easy process to run the Pi-Hole installation command found on the projects home page
- I have a PoE switch and was hoping to use that to power the Pi instead of having an additional power supplies & cables running everywhere. I found this handy PoE splitter that provides the necessary power to the Pi. It’s working like a charm!
- I was also interested in having a display on the Pi, so I bought a pair of these TFT displays and these enclosures that work nicely with them.
- To get the TFT display to work you need to install the driver found in LCD-show-170703.tar.gz by following the instructions found here.
- After the drivers are installed the Pi reboots and the display should start working.
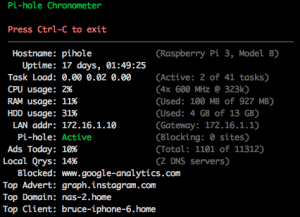
- To display the Pi-Hole stats I’m using the chronometer2 script.
- To select the appropriate font size for the display:
pi@pi-hole:~ $ sudo dpkg-reconfigure console-setup
- Encoding: UTF-8
- Character Set: Guess optional character set
- Font for the console: Terminus
- Font size: 8×14
- To prevent the display from going to sleep add ‘consoleblank=0’ to the end of /boot/cmdline.txt
Modifications to chronometer2
I like the basic concept of chronometer2 quite a bit, but I felt it could be improved upon slightly. For example, I don’t use my pi-hole as a DHCP server, so the few lines of the display showing it’s disabled is just wasted screen real estate as far as I’m concerned. I would much rather see the top client, top domain, and top advertiser that the original chronometer displays. I also wanted an easy way to be able to restart the chronometer2 display on my TFT display that didn’t require rebooting the whole Pi. When I’m tinkering with the chronometer2 script it’s annoying to keep rebooting the Pi and causing brief DNS outages on my network.
Given these thoughts I decided to make some tweaks to the script. Having spent years as a software developer I had one other small detail that I kept in mind – I didn’t want to change the default behavior in any way. So if you’re using the existing chronometer2 script and just drop my version into place on your pi-hole then you won’t see any difference unless/until you start playing with the new parameters I added. Without further ado, the parameters I added include:
-
- -f | –format <format_string>
This option lets you customize the display by being able to change the order of items that are displayed or even removing them. Each section of the display has been assigned an arbitrary letter. You just specify a format string in the order in which you want items displayed:
a : Logo
b: Pihole Information
c: Pihole Statistics
d: Network Details
e: DHCP Information
f: System Information
The default formatting string is simply ‘abcdef’, so if you don’t specify a custom format string then chronometer2 will use this value, which means the display will look exactly like the one you’re used to. If, like me, you don’t want to display the DHCP details then you would simply include ‘-f abcdf’ on the command line, leaving ‘e’ out of the format string.
- -t | –top
This will tell chronometer2 to include the top client/domain/advertiser information in the Statistics section of the display
- -p | –pid <filename>
This will write the PID (process ID) of chronometer2 to the specified file, making it easy to kill the script if you ever need to.
Why include the –pid option, you might ask? Good question! As I mentioned above, I wanted a way to be able to restart chronometer2 on my TFT display without having to reboot my Pi or doing any other tricky shenanigans. Most people set up their chronometer script to run out of /etc/profile or /home/pi/.bashrc by simply adding either ‘pihole -c’ or ‘./chronometer2.sh’ to the bottom of one of those files. Here’s how I have my .bashrc set up:
if [ "$TERM" == "linux" ] ; then
while :
do
/home/pi/chronometer2.sh $(cat /home/pi/chronometer2.cmdline)
sleep 1
done
fi
For those of you who aren’t terribly familiar with shell scripting, here’s a breakdown of what this does:
- chronometer2.sh is run only if the TERM environment variable is set to “linux”. This is what my Pi sets the TERM variable to when running chronometer2.sh locally on the TFT display. When I ssh into my Pi the TERM variable is set to “xterm”, so I’m not greeted by the chronometer2.sh script starting up every time I ssh into it.
- chronometer2.sh is run in an infinite loop (inside the while/do/done block). So if/when the script dies for any reason it will automatically restart after a one second delay.
- The script gets its command line arguments by reading them from the file /home/pi/chronometer2.cmdline each time it starts up.
The file /home/pi/chronometer2.cmdline looks like this:
-f abcdf -t -p /home/pi/chronometer2.pid
I also have a command called ‘killc2’ set up in my .bashrc:
alias killc2='kill $(cat /home/pi/chronometer2.pid)'
So now whenever I want to tinker with the chronometer2 script in any way I just edit the script and/or my chronometer2.cmdline file, invoke the command ‘killc2‘, and after a short pause the script restarts on the TFT display with the new parameters and any other changes I made.
My modifications to the chronometer2 script can currently be found here. If they’re merged into the official chronometer2 project I’ll update this to point there instead.
 emotion-phase
emotion-phase
emotion-phase